Fox Technologies: Your Ultimate Home Working Partner

At Fox Technologies, we are committed to providing our clients with top-notch home working solutions. We are a leading technology company located in Garforth, Leeds, England. Our team of experts is dedicated to providing customized solutions that meet the unique needs of our clients.
In this article, we will delve into the various home working services that we offer at Fox Technologies.
At Fox Technologies, we are committed to providing our clients with top-notch home working solutions. We are a leading technology company located in Garforth, Leeds, England. Our team of experts is dedicated to providing customized solutions that meet the unique needs of our clients.
In this article, we will delve into the various home working services that we offer at Fox Technologies.
VPN's
One of the most critical components of a successful remote work model is a Virtual Private Network (VPN). A VPN is a secure network connection that allows remote workers to access their organization's resources and data over the internet securely. With a VPN, employees can work from anywhere in the world while accessing their organization's network and resources as if they were in the office.
At Fox Technologies, we offer VPN solutions that are easy to use and secure. Our VPN solutions ensure that remote workers can access their organization's resources and data safely and securely. We provide our clients with robust security features, including encryption, multi-factor authentication, and firewall protection.
Our team of experts will work with you to customize your VPN solution to meet your organization's unique needs. Whether you need a site-to-site VPN for multiple remote workers or a point-to-point VPN for a single user, we've got you covered.
Microsoft Remote Desktop
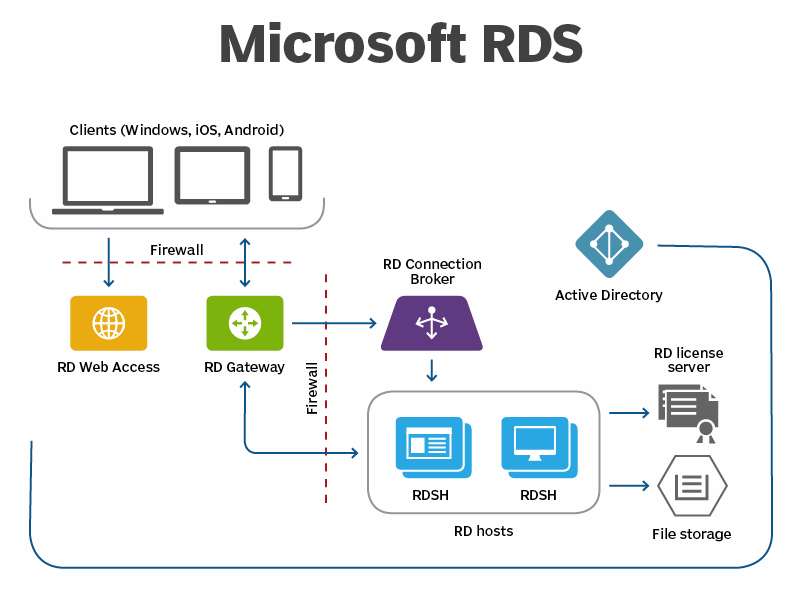
Another critical component of a successful remote work model is remote desktop access. Remote desktop access enables remote workers to access their desktops, applications, and files on their organization's network from any device with an internet connection.
At Fox Technologies, we offer Microsoft Remote Desktop solutions that are easy to use and secure. Our Microsoft Remote Desktop solutions enable remote workers to access their organization's resources and data as if they were in the office. Our solutions ensure that remote workers can collaborate seamlessly, share files, and access applications securely.
We provide our clients with robust security features, including encryption, multi-factor authentication, and firewall protection. Our team of experts will work with you to customize your Microsoft Remote Desktop solution to meet your organization's unique needs. Our courier Swapped Out service ensures your employees are never left without fully functioning equipment to carry out their tasks.
At Fox Technologies, we understand that laptops and PCs are essential tools for remote workers. We also understand that sometimes, these devices break down, and remote workers need them fixed quickly to get back to work.
We offer courier services that enable remote workers to send their laptops and PCs to us for repair. Our team of experts will diagnose and repair the device, ensuring that it is back up and running as quickly as possible.
We understand that downtime can be costly for organizations, which is why we strive to provide fast and efficient repair services. Our courier services ensure that remote workers can get their devices fixed without leaving their homes, saving them time and money.
Our courier services also ensure that remote workers can send their devices securely. We provide our clients with robust security features, including encryption, multi-factor authentication, and firewall protection, to ensure that their devices are safe and secure during transit.
Conclusion
At Fox Technologies, we are committed to providing our clients with top-notch home working solutions. Our VPN solutions, Microsoft Remote Desktop solutions, and courier services are designed to meet the unique needs of our clients.
We are located in Garforth, Leeds, England, and we serve clients in the UK and beyond. Our team of experts is dedicated to providing customized solutions that guarantee seamless collaboration and productivity for remote workers.
If you're looking for a reliable home working partner, look no further than Fox Technologies. Contact us today